Cyble Vision
UX Case Study
UX Case Study
Privacy Policy Notice
Due to confidentiality and privacy policies at Cyble, this case study provides a high-level overview of my contributions to the Cyble Vision project without disclosing specific design details.
Problem Definition
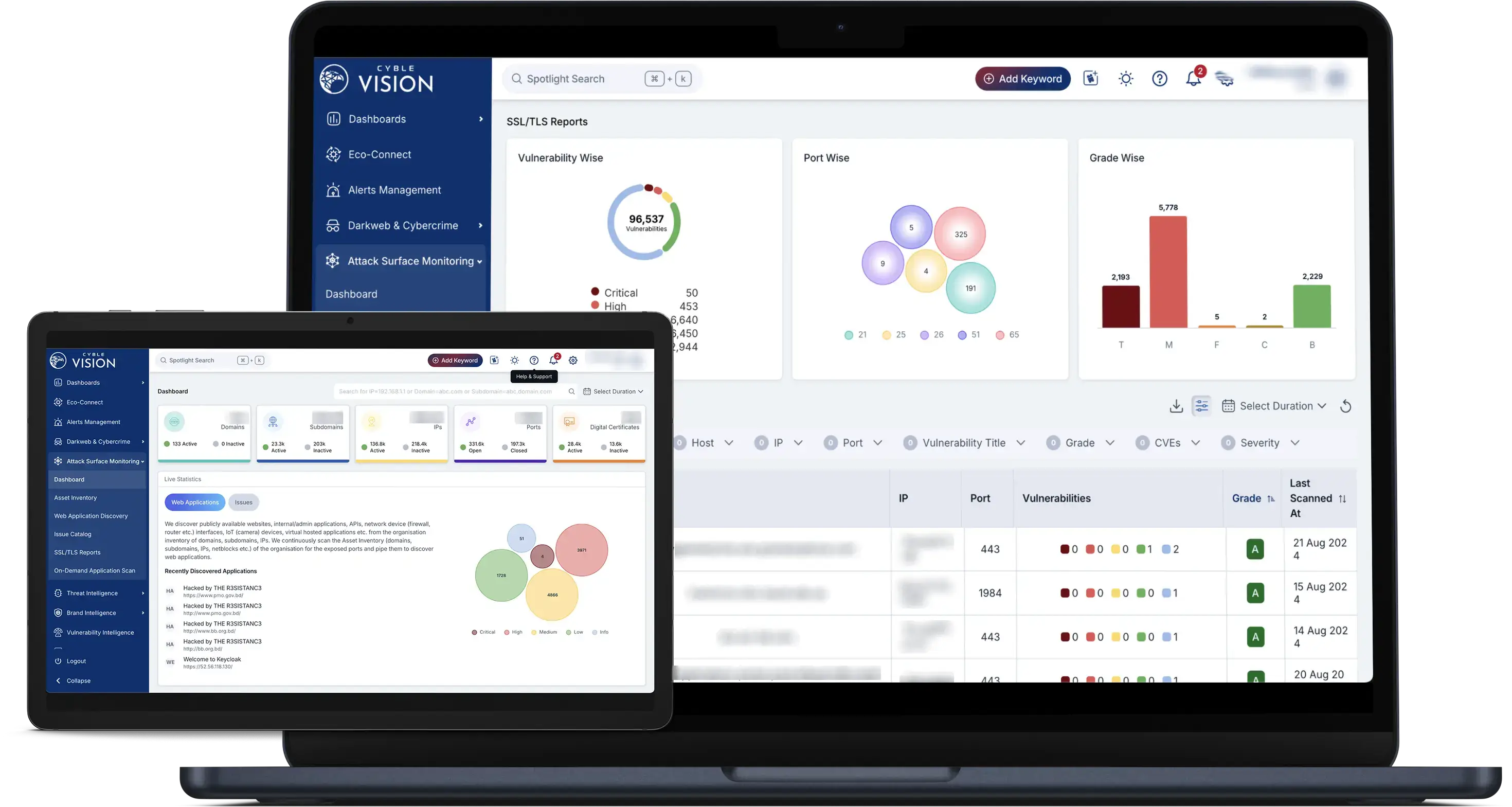
Cyble Vision is an AI-powered cybersecurity platform designed to help companies proactively detect and respond to security threats. As the product evolved, it encountered several challenges related to performance, user experience, and the integration of complex features. The primary goal was to improve the usability and efficiency of the platform, ensuring it met the needs of cybersecurity professionals while keeping up with the technical complexity required for real-time threat detection.
Key Challenges:
- Performance bottlenecks:The app’s load time was too long, affecting user productivity.
- Complex navigation and feature access: Users struggled with navigating the platform’s dense information architecture and accessing critical features.
- Feature integration:As more tools were added to the platform, maintaining intuitive usability became increasingly difficult.
- Collaborative alignment:Aligning design decisions with Cyble’s engineering team and business stakeholders was crucial to ensure solutions were technically viable and aligned with the business strategy.
Team Collaboration:
The process involved frequent meetings with engineers, product managers, and stakeholders to deeply understand the platform’s technical and business needs. We had to navigate technical constraints while meeting aggressive timelines, ensuring that the designs were both feasible and effective.
Design Process
The design process at Cyble was grounded in agile methodology, allowing for quick iterations and continuous feedback. By working closely with the technical and product teams, I ensured that the solutions developed were both user-centered and technically feasible. The design process unfolded in multiple phases:
Phase 1: Research and Discovery
To start, I conducted a thorough analysis of the existing Cyble Vision platform, mapping the user journey and identifying pain points. This involved:
- User Research: Gathering qualitative and quantitative data from users through interviews, surveys, and usage analytics.
- Stakeholder Workshops: Working with Customer Success Managers (CSMs), Sales, and cybersecurity experts to understand business needs and priorities.
- Technical Feasibility Discussions: Collaborating with engineers to identify technical constraints and opportunities, ensuring designs would work seamlessly within the existing architecture.
Outcomes from Discovery:
Phase 2: Defining Design Goals and Requirements
Based on the discovery phase, we defined a set of design objectives that would guide the rest of the project:
- Performance Optimization: Speed up load times and reduce system lag to improve overall user experience.
- Streamlined Navigation: Redesign the information architecture to make it easier for users to find key features.
- Intuitive Data Visualization: Improve the way complex cybersecurity data is presented to allow for quicker analysis.
- Modular and Scalable Designs: Ensure that new features could be added to the platform without cluttering the user interface or decreasing usability.
Phase 3: Ideation and Wireframing
With clear objectives, I moved into the ideation phase, exploring different ways to address the issues identified. The focus was on rapid iteration, testing concepts quickly and refining them based on feedback from stakeholders and users.
- Wireframes and Sketches: Low-fidelity wireframes were created to explore different layouts and workflows for the platform’s core features. I utilized design thinking workshops with both the design and engineering teams to refine these ideas.
- Prototyping: Mid-fidelity interactive prototypes were developed to validate the navigation and feature integration ideas. These prototypes were used to run usability tests with users to gather feedback on navigation flow, feature accessibility, and data visualization clarity.
Phase 4: Design System and Component Creation
To ensure scalability, I led the creation of a unified design system for Cyble Vision, which included:
- Modular Components: Designing reusable components for UI elements such as buttons, cards, tables, and form fields.
- Responsive Layouts: Ensuring the platform performed seamlessly across devices, particularly for cybersecurity professionals who need mobile access.
- Consistency: Maintaining uniformity in visual language, typography, color palettes, and interaction patterns across different modules, reducing development time and improving user experience.
Phase 5: User Testing and Feedback
With high-fidelity prototypes in place, I ran multiple rounds of user testing. This phase focused on:
- Usability Testing: Observing how users interacted with the redesigned platform and gathering feedback on ease of use, speed, and intuitiveness.
- Performance Benchmarking: Collaborating with engineers to test system performance with the new designs, ensuring load times were significantly reduced and the platform remained responsive.
- Feedback from Stakeholders: Frequent sessions with business stakeholders ensured that the designs aligned with Cyble’s strategic goals. Product managers helped prioritize features, while sales teams provided input on how the designs could support client needs.
User
Persona

Name: Alex Turner
Age: 35
Job Title Senior Cybersecurity Analyst
Experience Level: 10+ years in cybersecurity
Location: New York, USA
Background:
- Education: Bachelor’s Degree in Information Technology, Certified Ethical Hacker (CEH), Certified Information Systems Security Professional (CISSP).
- Professional Experience: Alex has been working in cybersecurity for over 10 years and is currently employed at a large financial institution. He leads a team of analysts responsible for protecting the company from emerging threats, conducting real-time threat monitoring, and responding to incidents.
- Industry: Financial Services
- Tech Proficiency: Highly skilled in security platforms, advanced threat intelligence systems, penetration testing, and data visualization tools.
Goals and Needs:
- AProactive Threat Detection: Stay ahead of emerging cyber threats to protect the organization’s data and assets.
- Streamlined Threat Analysis: Quickly identify, analyze, and respond to potential threats using a tool that aggregates large datasets and provides actionable insights.
- Optimized Incident Response: Reduce response times to critical security incidents by accessing relevant data in an intuitive and fast-paced environment.
- SCollaborate Efficiently: Work with internal teams, external partners, and vendors to resolve issues swiftly, ensuring the organization stays secure.
Challenges:
- Complex Data Handling: Alex often struggles with platforms that make it difficult to access, analyze, and visualize large datasets related to cybersecurity incidents.
- Time-Pressure Situations: He frequently works under pressure, needing to respond to threats in real-time with little room for error. Slow or unresponsive tools hinder his performance.
- Overloaded with Features: Some cybersecurity tools are overloaded with complex features that are difficult to navigate, especially in time-sensitive scenarios.
- Collaboration Gaps: Managing communications with different teams—IT, Customer Success, and external partners—can be difficult without a streamlined issue-tracking system.
Empathy Mapping
Outcomes
Pain Points:
- Slow System Performance:Long load times can frustrate Alex, particularly when trying to access critical threat intelligence data during a security breach.
- Overcomplicated UI: Complex navigation systems and unnecessary features add to cognitive overload, making it harder for him to focus on solving urgent issues.
- Inconsistent Data Visualizations:Inaccurate or unclear visual representations of data can delay threat identification and increase the chances of security breaches.
- Manual Workflows:Without automated processes, Alex often spends time manually managing user roles, permissions, or incident tracking, detracting from more critical tasks.
Motivations
- Security Leadership: Alex is motivated by the desire to lead his team in providing top-tier security for his organization. He values tools that enhance his ability to mitigate threats quickly.
- Efficiency: He wants to use tools that reduce his workload, allowing him to focus on critical tasks like threat analysis, rather than being bogged down by administrative tasks.
- Continuous Improvement: Alex is constantly looking for ways to improve his skills and processes, staying up-to-date with the latest threats and cybersecurity best practices.
Key Design Decisions
- Redesigning the Dashboard:A cleaner, more intuitive layout was introduced for Cyble Vision’s main dashboard. Critical security data, like threat alerts and actor newsfeeds, were made more prominent, reducing the cognitive load for users.
- Reworking Navigation: A new navigation structure was designed to make accessing frequently used features faster. By introducing a side navigation bar and an improved search system, users could locate tools like the Threat Intelligence Module or Incident Tracker in fewer clicks.
- Data Visualization Overhaul:Given the complexity of the data, we reworked the data visualization framework. Heat maps, timelines, and interactive charts were introduced to help users make sense of large datasets more easily. Additionally, loading times for large data sets were reduced, improving the speed of threat analysis.
Key Results After Usability Testing
- Users reported a 30% increase in satisfaction with the platform’s performance and usability.
- Navigation times were significantly reduced, allowing users to find key features in 40% fewer clicks.
- Threat analysis times dropped by 25%, as users could now access and interpret data more quickly.
Outcomes and Impact
The revamped platform delivered significant improvements in both performance and user engagement:
- Performance: Reduced load times from 45 seconds to 4 seconds, significantly improving user productivity.
- Data Visualization: The redesign of critical components and dashboards led to a 40% boost in user engagement and improved decision-making efficiency.
- User Retention and Onboarding:The creation of the My Ecosystem and MSSP Dashboard for partner companies helped increase client onboarding by 70% and retain 35% of partner companies.
- Scalability:The new design system allowed the seamless addition of features like the IAM Flow for managing roles and permissions, reducing manual customer success work by 65%.
Challenges Faced
While the project was successful, several challenges emerged:
- Balancing complexity and usability: Cybersecurity data is inherently complex, and simplifying this data without losing its nuance was a continuous challenge.
- Tight deadlines: The fast-paced nature of Cyble required quick iterations and frequent deliverables. This often meant balancing speed with precision and quality.
- Technical limitations:Some features had to be scaled back or adjusted to fit within the platform’s existing infrastructure. Close collaboration with engineers was necessary to find feasible solutions without compromising user experience.

Key Learnings
While the project was successful, several challenges emerged:
- Agile Methodology Works: The iterative, agile approach allowed for flexibility and constant improvements based on real-time feedback, ensuring that the final product was user-centered.
- Collaboration is Crucial: Close collaboration with technical teams ensured that all designs were feasible, performant, and scalable.
- Importance of a Design System:The creation of a design system was instrumental in maintaining consistency across the platform and speeding up future design and development work.